title
Please take a moment to fill out this form. We will get back to you as soon as possible.
All fields marked with an asterisk (*) are mandatory.
F5 Training Courses
Expand your technical skills in application delivery networking, application availability & performance, multi-cloud management, application security, network security, access & authorization, and online fraud prevention with our F5 authorized training courses.

IBM Learning Subscription from $3,495
Gain unlimited access to a vast digital library and benefit from tailored instructional training.
Browse All Topics
Browse our full curriculum of F5 training and certification courses. Learn how to optimize BIG-IP solutions for application delivery and infrastructure security.

F5 Training and Certification Through LearnQuest
F5 Networks is the global leader in application services and delivery networking. F5 provides load balancing, security, performance optimization and availability enhancement for critical business applications. Their robust technology solutions include BIG-IP modules like Access Policy Manager, Advanced Firewall Manager, and Local Traffic Manager. These offerings allow enterprises and service providers to optimize, secure, and scale delivery of their apps and networks. With over 50% market share, F5 BIG-IP delivers industry-leading application traffic management, control, and protection.
LearnQuest offers comprehensive training courses that give IT professionals hands-on skills for deploying and managing F5's powerful application delivery and security solutions. With classroom labs and real-world practical exercises, LearnQuest's expert instructors provide role-based education on installing, configuring, managing, and maximizing F5 modules like Access Policy Manager, Advanced Firewall Manager, and Local Traffic Manager.

The Value of F5 Training
Taking F5 training and certification courses provides significant benefits for IT professionals and their organizations:
- Gain hands-on experience to build real-world skills - F5 training provides practical labs and scenarios to develop the skills needed in real-world environments.
- Develop expertise to effectively manage and optimize F5 solutions - Courses deliver the knowledge to properly install, configure, manage, and troubleshoot F5 products for maximum efficiency.
- Shorten deployment times by accelerating admin proficiency - Hands-on learning accelerates proficiency with F5 solutions, enabling faster rollouts and time to value.
- Increase IT team productivity and efficiency - Training tailored to job roles equips teams to work faster and more confidently with F5 technologies.
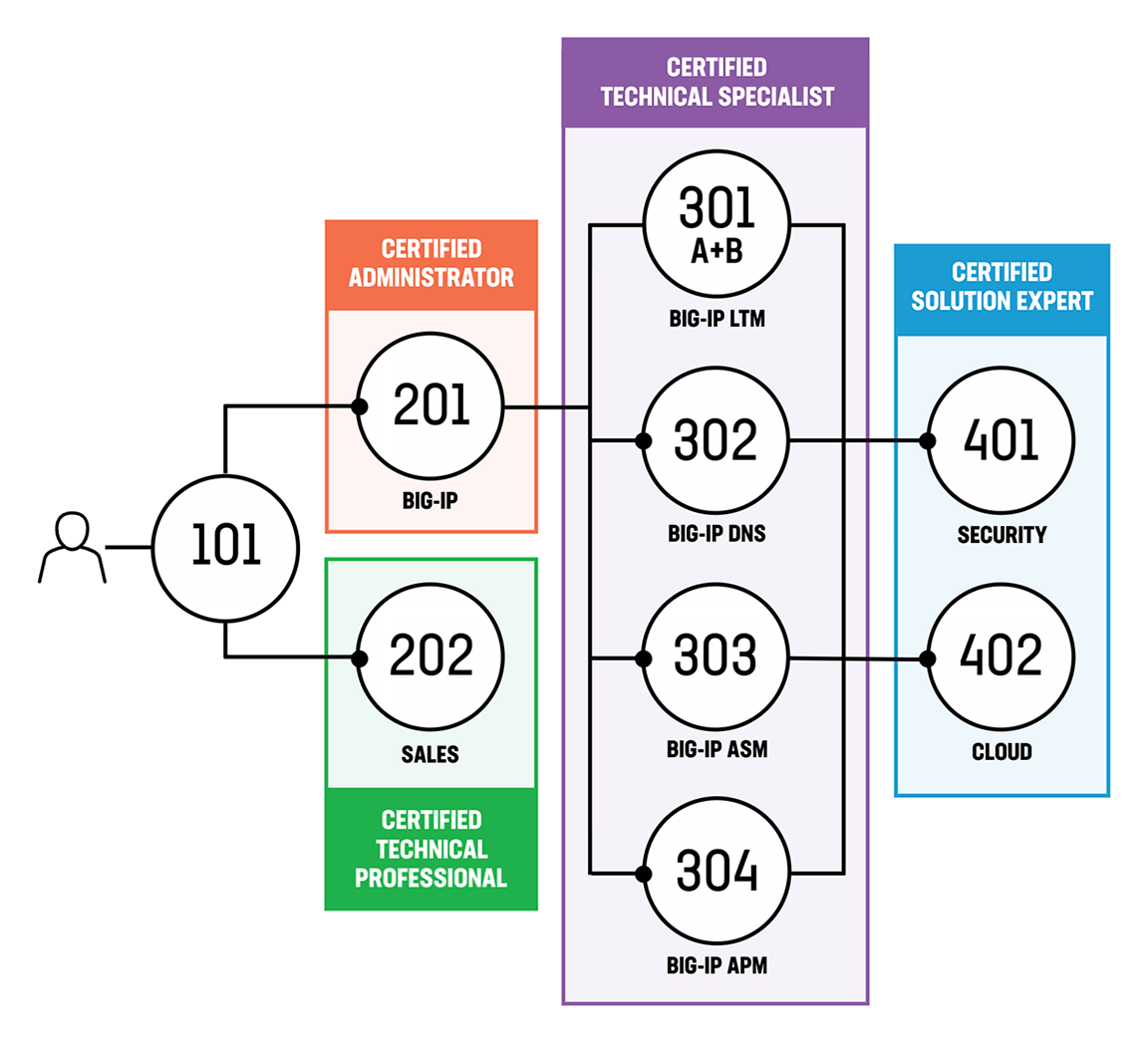
F5 Certification Tracks
F5 Networks offers four certification tracks tailored to different IT roles and skill levels:
- Administrator - Validates core skills to manage, maintain, and troubleshoot installed F5 solutions.
- Technical Professional - Demonstrates deeper expertise with specific F5 products and integrations.
- Technical Specialist - Validates expert-level skills to implement and optimize specific F5 modules and architectures.
- Solution Expert - Demonstrates expert abilities to design and architect complex solutions across multiple F5 and third-party products.
The segmented certification paths allow professionals to pursue targeted training and validation for specialized F5 administration, engineering, technical, and architecture roles.
Upskilling with LearnQuest for Your Organization
LearnQuest provides customized F5 training solutions to enhance your team's skills and drive business outcomes. Our comprehensive programs integrate online learning, live sessions, and practical labs to rapidly develop proficiency in F5 technologies.
We will collaborate with you to design a personalized plan that aligns with your specific requirements.
Partner with us to establish an F5 Center of Excellence. Contact LearnQuest today for a complimentary consultation on empowering your team to excel in application delivery and security.
Contact Us For A Free Consultation
Frequently Asked Questions
-
What F5 training courses do you offer?
We offer a range of authorized F5 training including courses on BIG-IP modules like Access Policy Manager, Advanced Firewall Manager, and Local Traffic Manager. See our full curriculum.
-
What skills will I gain from your F5 training?
Our hands-on courses will teach you to install, configure, manage, troubleshoot, and optimize F5 solutions for application delivery and infrastructure security.
-
What formats are available for F5 training?
We provide flexible training formats including live online, virtual classroom, onsite, and self-paced online courses.
-
How can F5 training benefit my organization?
F5 training can upskill your team with hands-on expertise to shorten deployment times, boost efficiency, and maximize your use of F5 technologies.
-
Do you offer official F5 certification exam prep?
Yes, our training will fully prepare you to pass F5 certification exams like the F5 Certified BIG-IP Administrator test.
-
What level of experience do I need for F5 courses?
We offer F5 courses for all levels. Some foundational knowledge of networking and application delivery may help understand concepts faster.
-
Can I take just one F5 course or do I need the whole curriculum?
You can take a single stand-alone F5 course for a focus on one module or product. Bundles offer discounts.
-
Are there prerequisites for any F5 courses?
Some advanced courses may require knowledge from our introductory F5 courses. Check individual course pages for details.
-
Who are the F5 instructors?
Our instructors are certified F5 specialists with deep real-world experience designing, deploying, and managing F5 solutions.
Need more Information?
Speak with our training specialists to continue your learning journey.
Talk to our team






